Documentation Index
Fetch the complete documentation index at: https://docs.snapsec.co/llms.txt
Use this file to discover all available pages before exploring further.
Overview
The Active Vulnerabilities section provides a real-time view of all open security findings across your organization. It is the primary workspace for:- Triage and prioritization
- Assignment and ownership
- Tracking remediation progress
- Managing vulnerability lifecycle
Vulnerability Dashboard
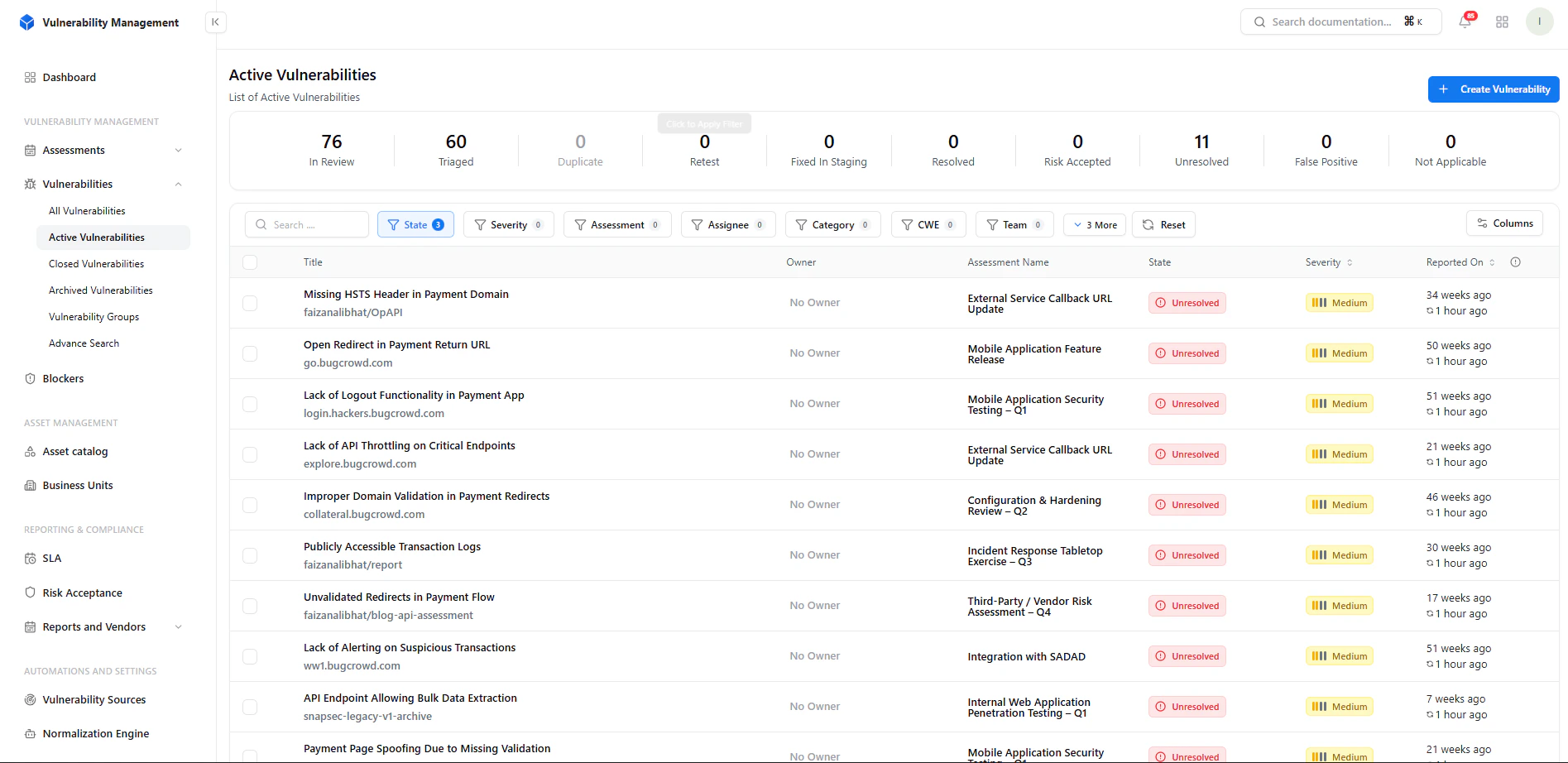
Key Metrics
- In Review → Newly identified findings awaiting triage
- Triaged → Reviewed and categorized
- Duplicate → Repeated findings grouped
- Retest → Awaiting verification after fix
- Fixed in Staging → Patched but not yet verified
- Resolved → Successfully remediated
- Risk Accepted → Accepted by business
- Unresolved → Still open
- False Positive → Invalid findings
- Not Applicable → Out of scope
Filtering & Search
Available Filters
- State
- Severity
- Assessment
- Assignee
- Category
- CWE
- Team
- Focus on critical issues
- View team-specific vulnerabilities
- Filter by compliance or category
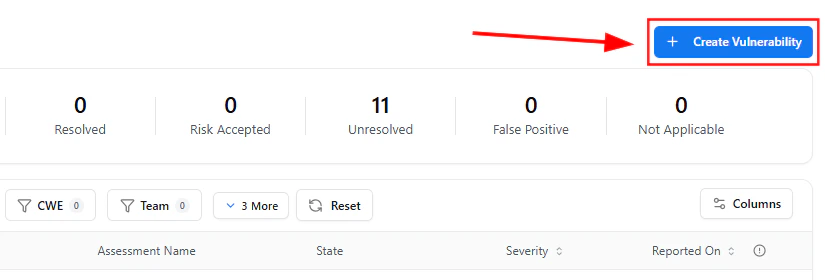
Create Vulnerability
- Manual testing
- External reports
- Bug bounty submissions
Required Fields
- Vulnerability Title
- Assessment Selection
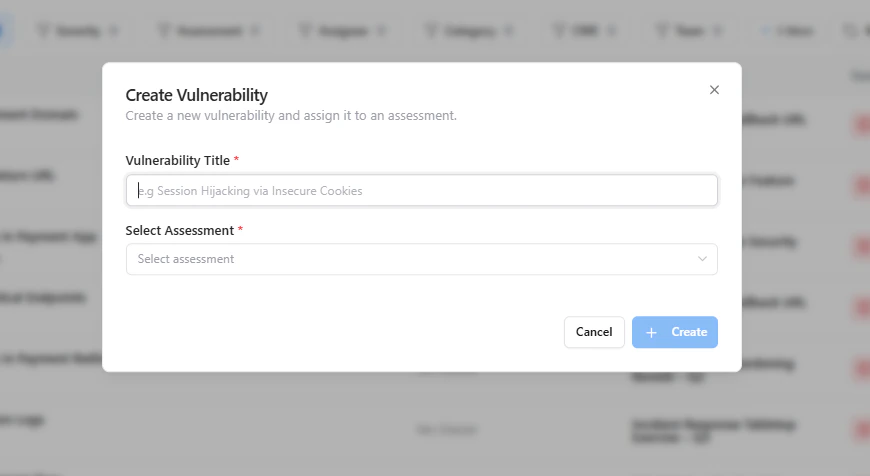
Vulnerability Details View
Report Includes
- CWE mapping
- Category classification
- Detailed description
- Steps to reproduce
- Impact analysis
- References (OWASP, CWE, etc.)
Metadata & Ownership
Fields Available
- Owner → Assigned individual
- State → Current lifecycle stage
- Assessment → Linked assessment
- Collaborators → Supporting users
- Affected Asset → Impacted system
- CWE Mapping → Standard classification
- Reported Date
- Business Unit
- SLA Status
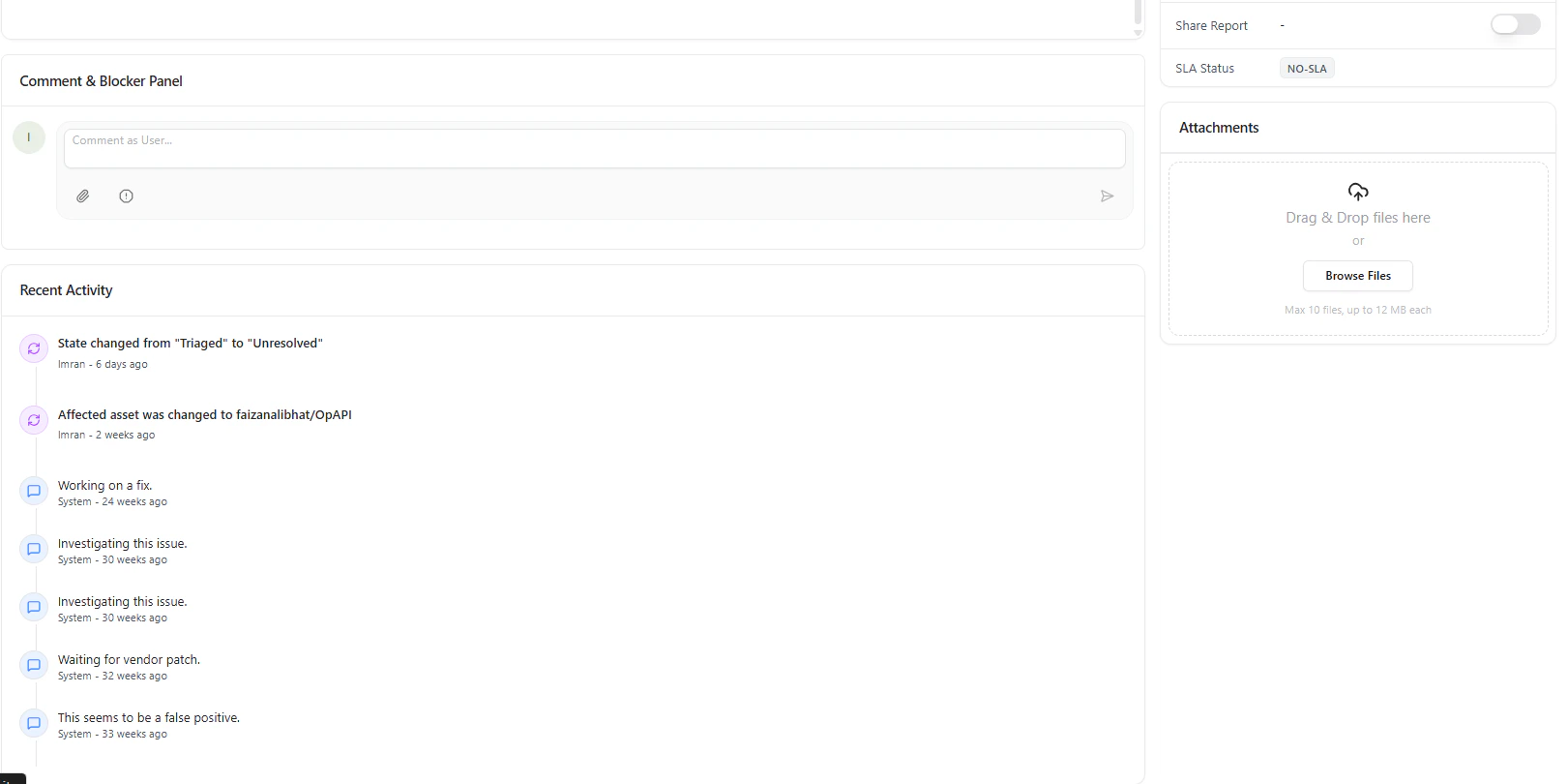
Collaboration & Activity
Each vulnerability includes:- Comments panel → Team discussion
- Blockers → Identify dependencies
- Activity timeline → Full audit trail
- Who changed what
- When actions were taken
- Progress toward remediation
Attachments
Upload supporting evidence:- Screenshots
- Request/response logs
- Exploit proof
Why This Matters
This is where vulnerability management becomes operational.Key Benefits
- Centralized vulnerability lifecycle management
- Faster triage and prioritization
- Clear ownership and accountability
- Full audit trail for compliance
- Improved remediation tracking
Where It Fits
Active Vulnerabilities connects with:- Assessments → Source of findings
- Detection Rules → How issues are identified
- Vulnerability Sources → Confidence & accuracy
- SLA Module → Remediation timelines
- Reports → Executive visibility
Explore Live Demo
Manage Vulnerabilities End-to-End
Track, triage, and resolve vulnerabilities efficiently across your organization.