Overview
The Lifecycle Management module allows teams to control how assets transition across different operational states — from staging to decommissioning — while maintaining full visibility and context. It ensures assets are never lost, supports recovery when needed, and preserves security and ownership data across the entire lifecycle.Staged Assets
Key Behavior
- Assets can be reviewed before activation
- Prevents unverified assets from entering active inventory
- Displays an empty state when no assets are staged
Decommissioned Inventory
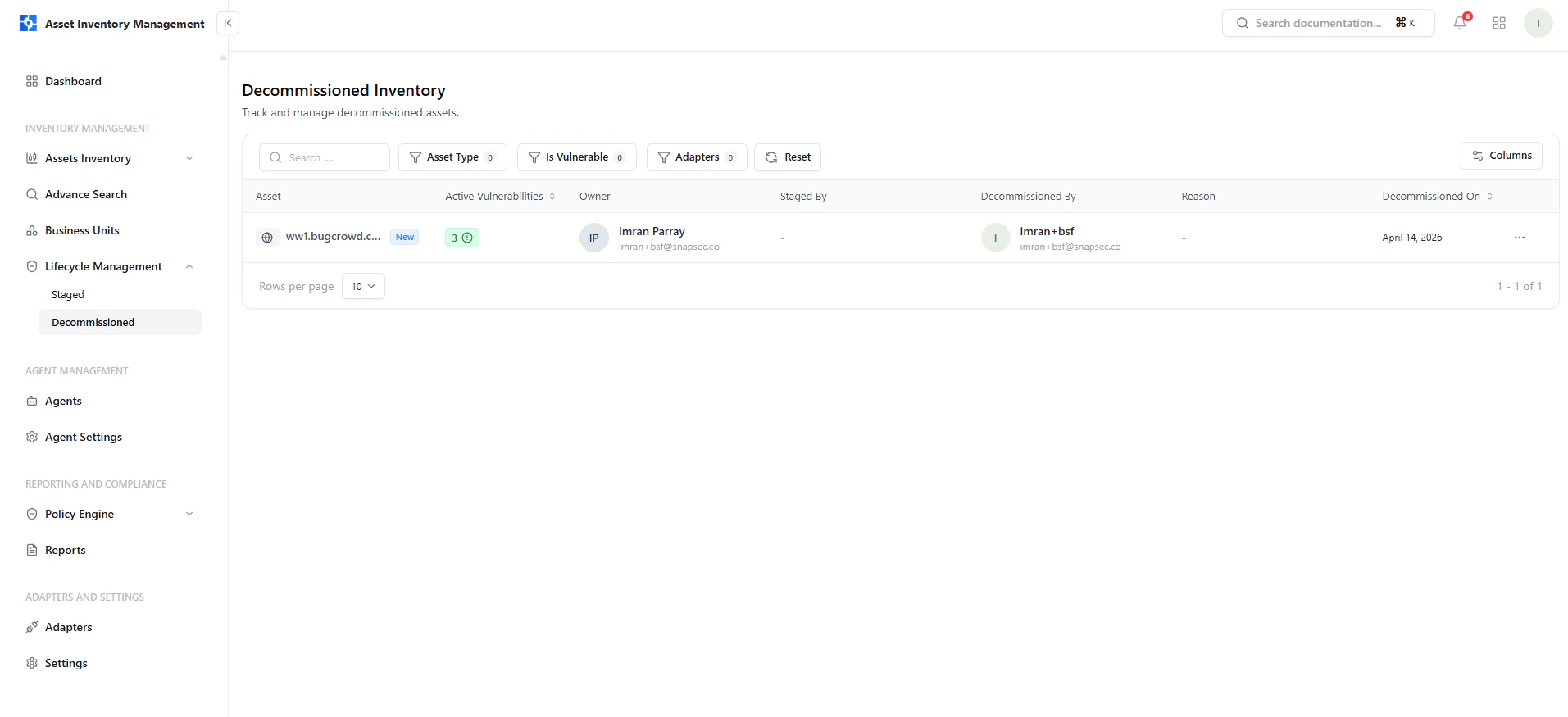
What You Can See
- Asset name and type
- Active vulnerabilities at time of decommission
- Owner and ownership details
- Who decommissioned the asset
- Decommission date
Restoring Assets
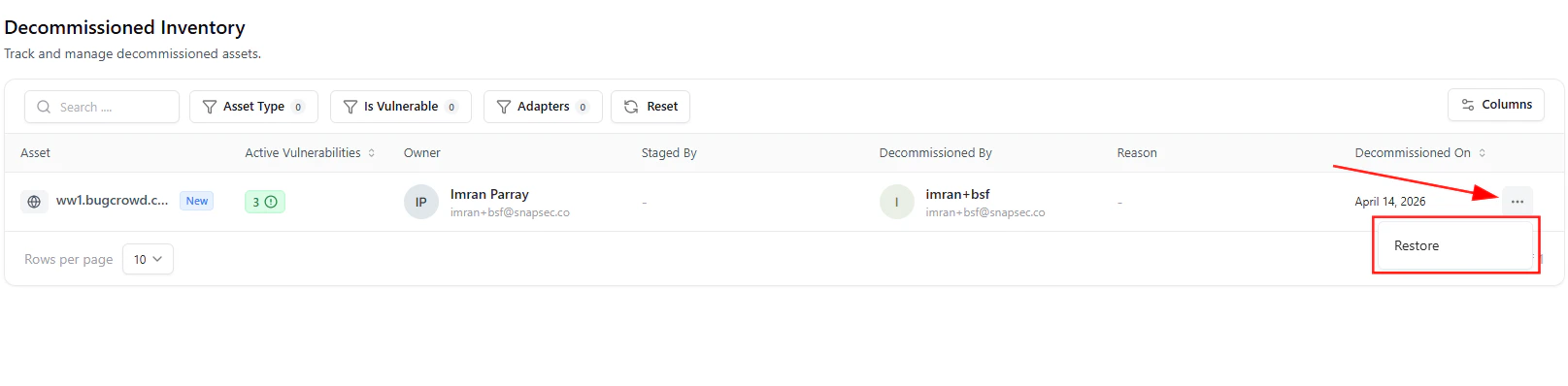
How It Works
- Click the three-dot menu (⋯)
- Select Restore
- Asset returns to active inventory
Lifecycle State Control
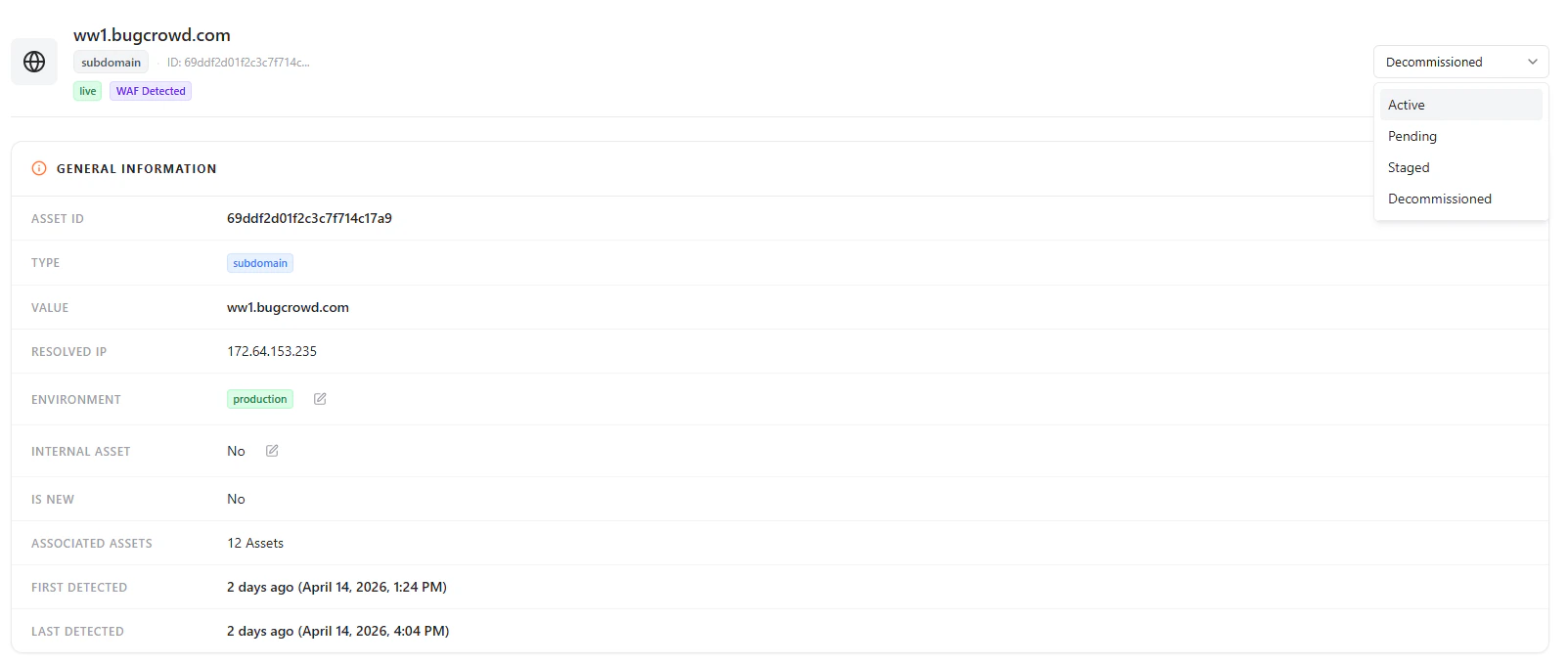
Available States
- Active — Fully operational and monitored
- Pending — Newly discovered and under review
- Staged — Prepared but not yet active
- Decommissioned — Retired but retained for visibility
General Asset Information
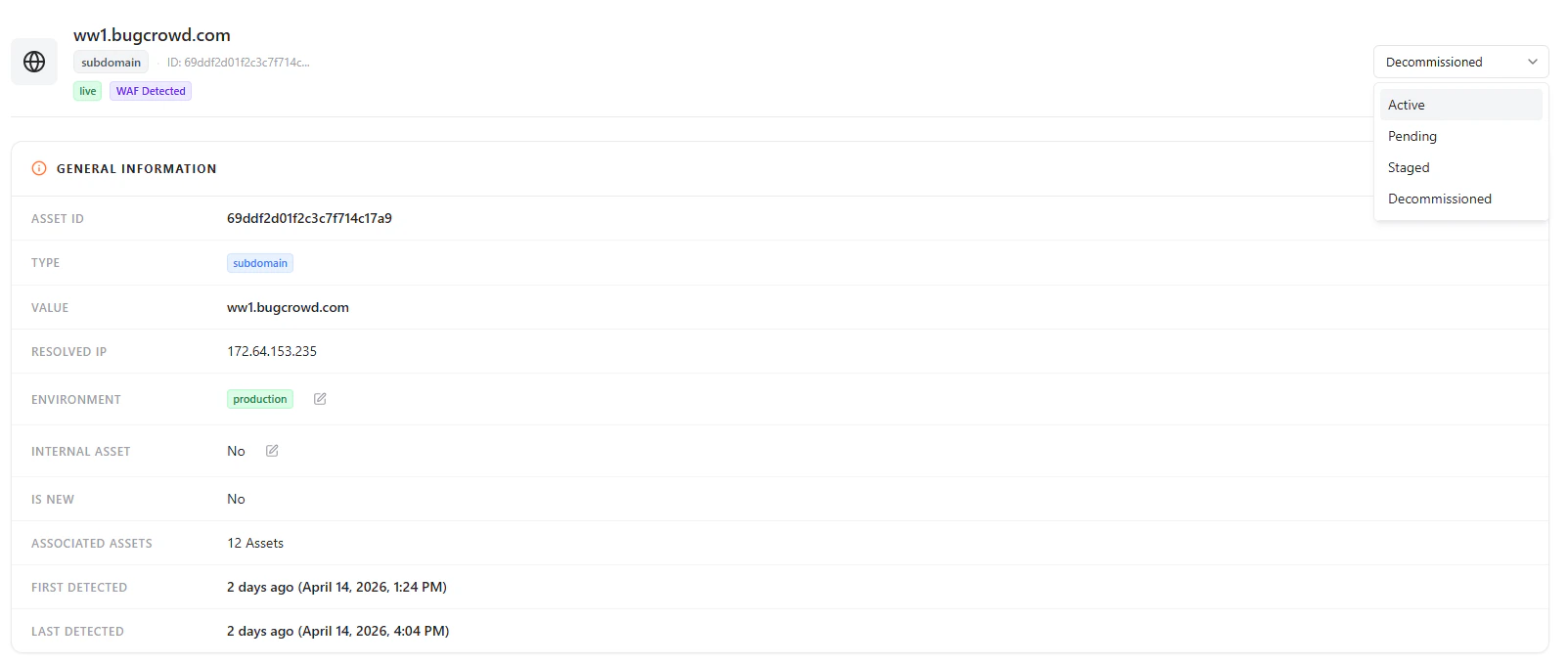
Includes
- Asset ID and type
- Asset value (domain/IP)
- Environment classification
- Internal vs external designation
- Associated assets
- First and last detection timestamps
Subdomain & Exposure Details
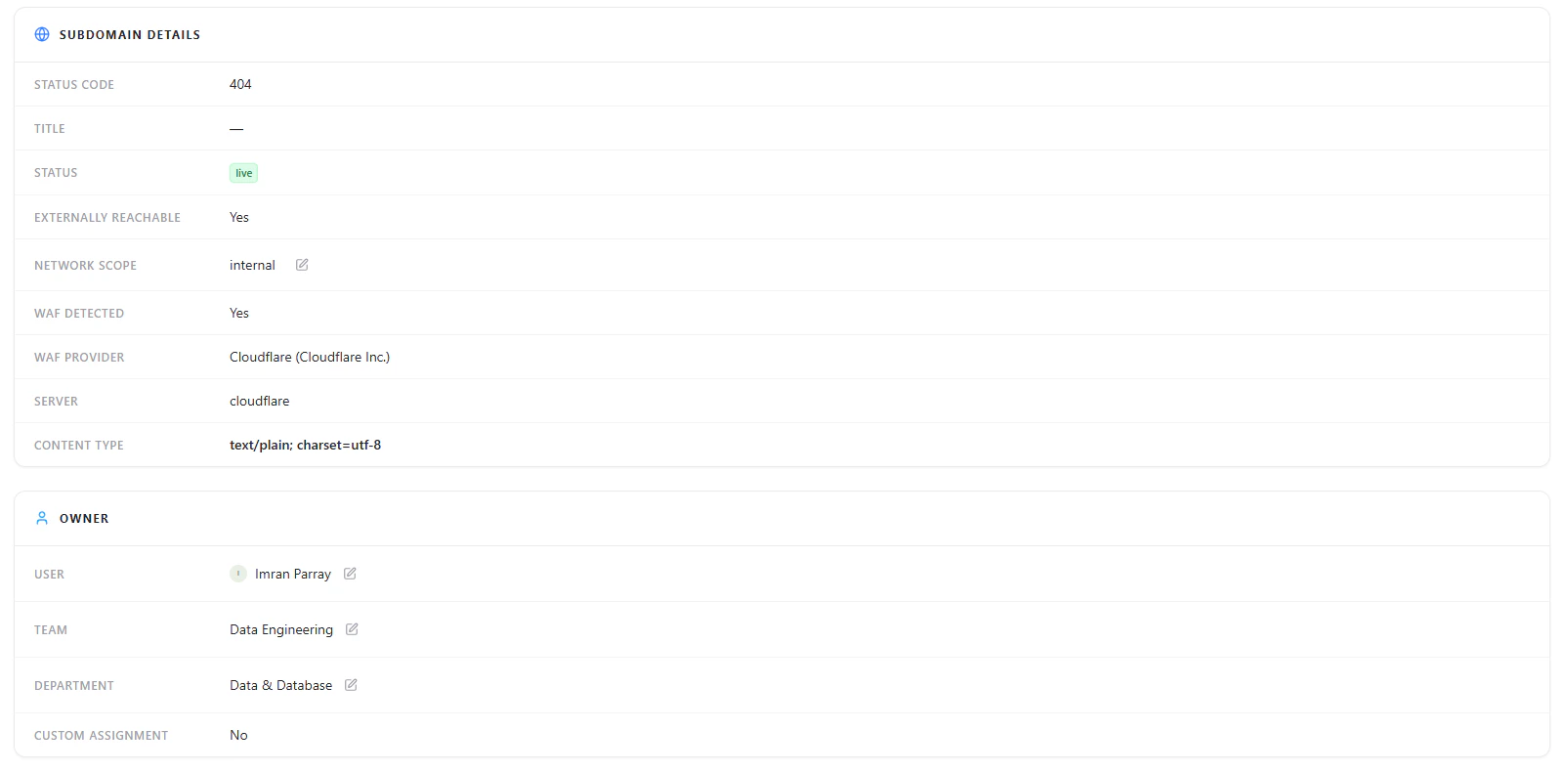
Key Insights
- HTTP status code
- External reachability
- WAF presence and provider
- Network scope
Ownership & Accountability

Includes
- Assigned user
- Team
- Department
- Custom assignment status
Location & Infrastructure Data
Data Points
- City, region, country
- Latitude and longitude
- ISP and ASN
- Organization and timezone
- IP version and exposure
Security Overview
Includes
- Total vulnerabilities
- Severity breakdown (Critical, High, Medium, Low, Info)
- Open vs closed vulnerabilities
- Aggregate CVSS score
- Remediation progress
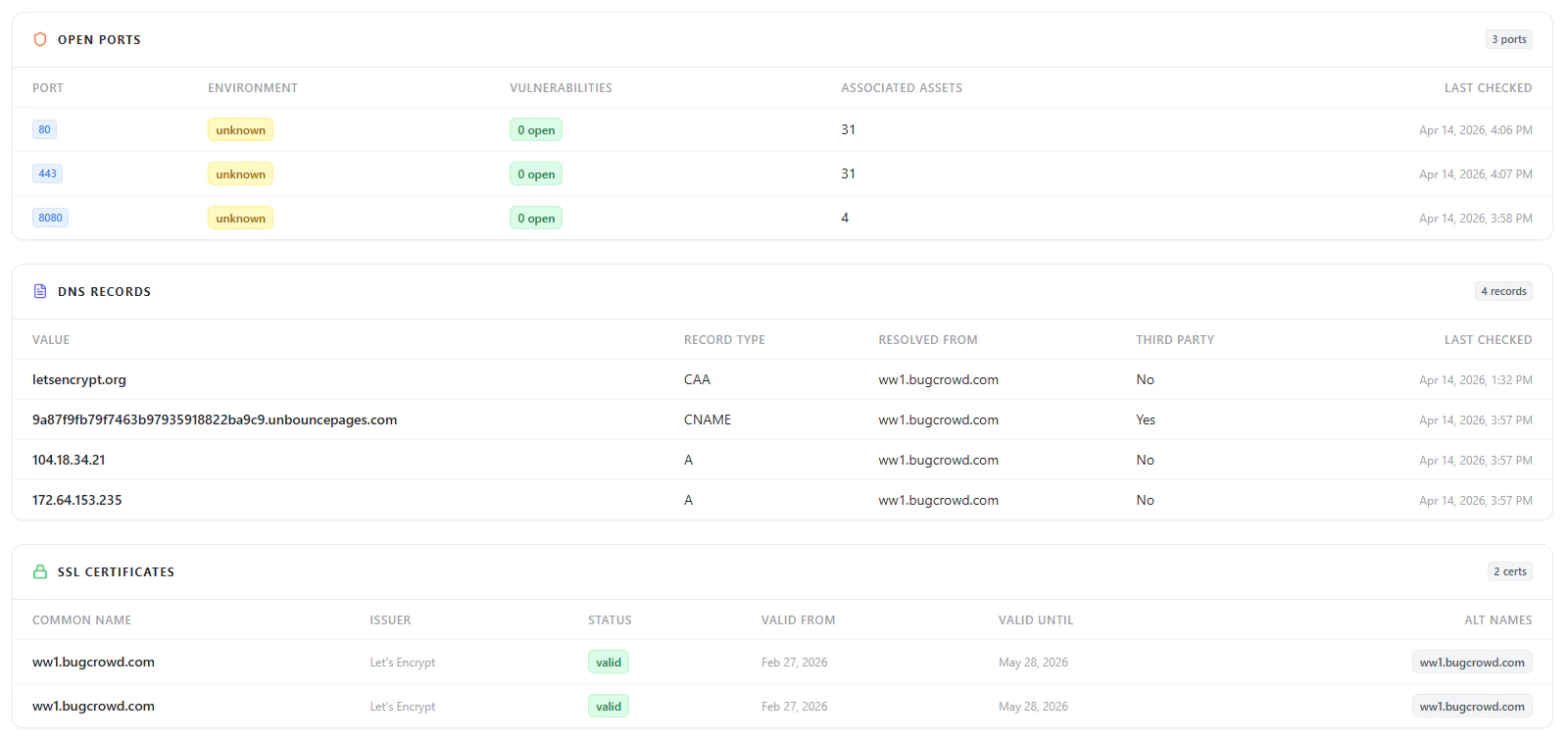
Open Ports
DNS Records
SSL Certificates
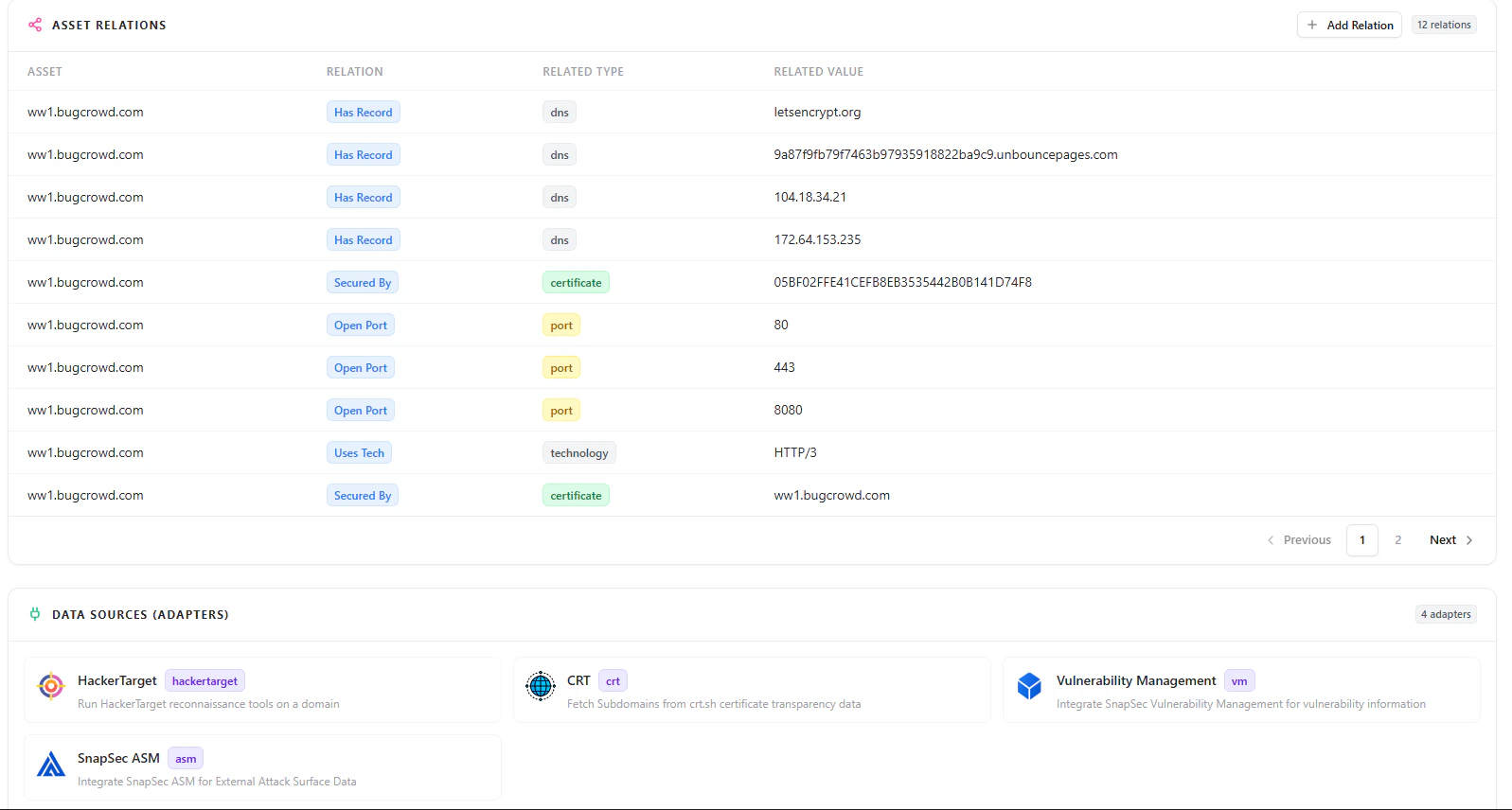
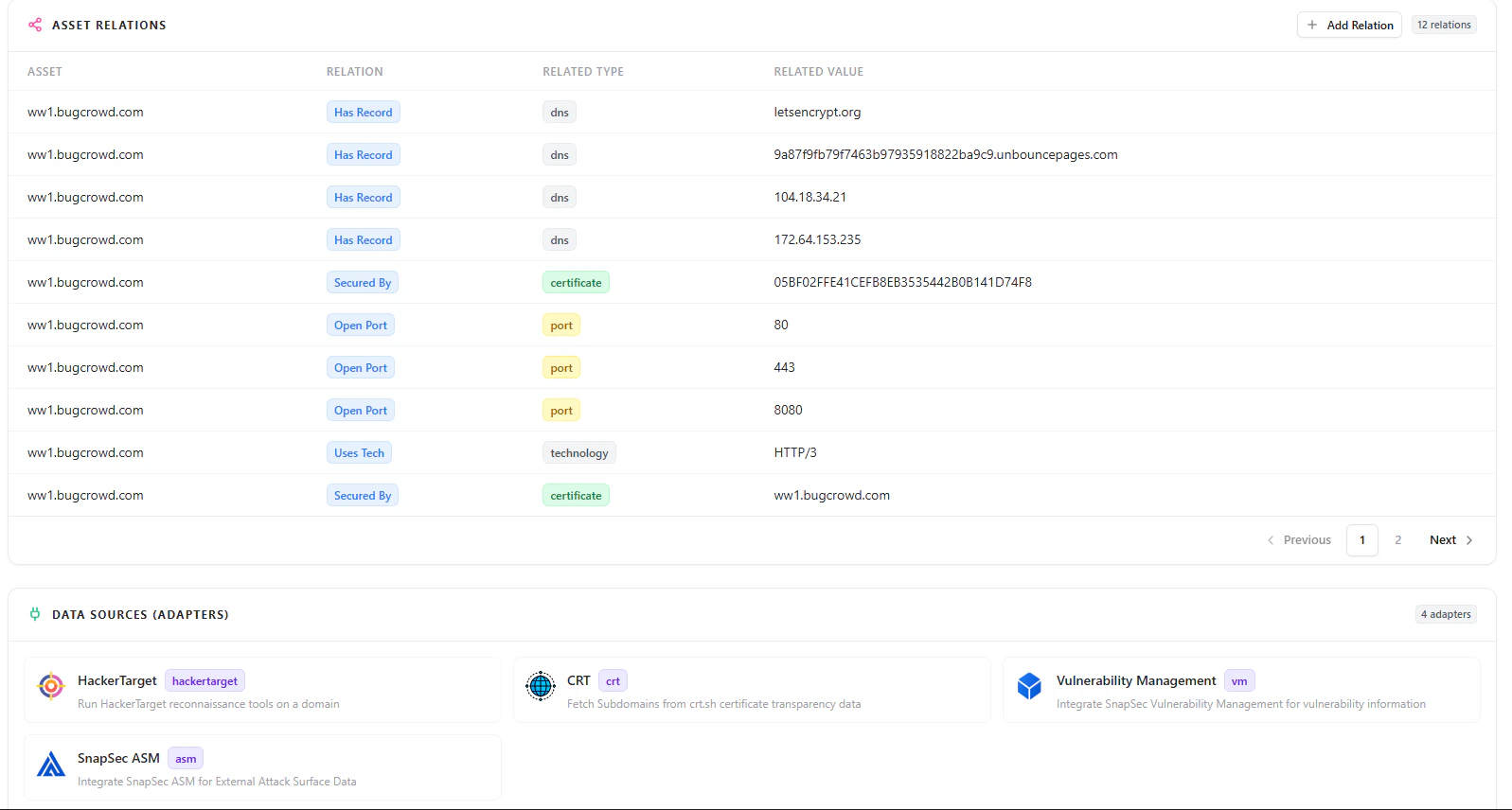
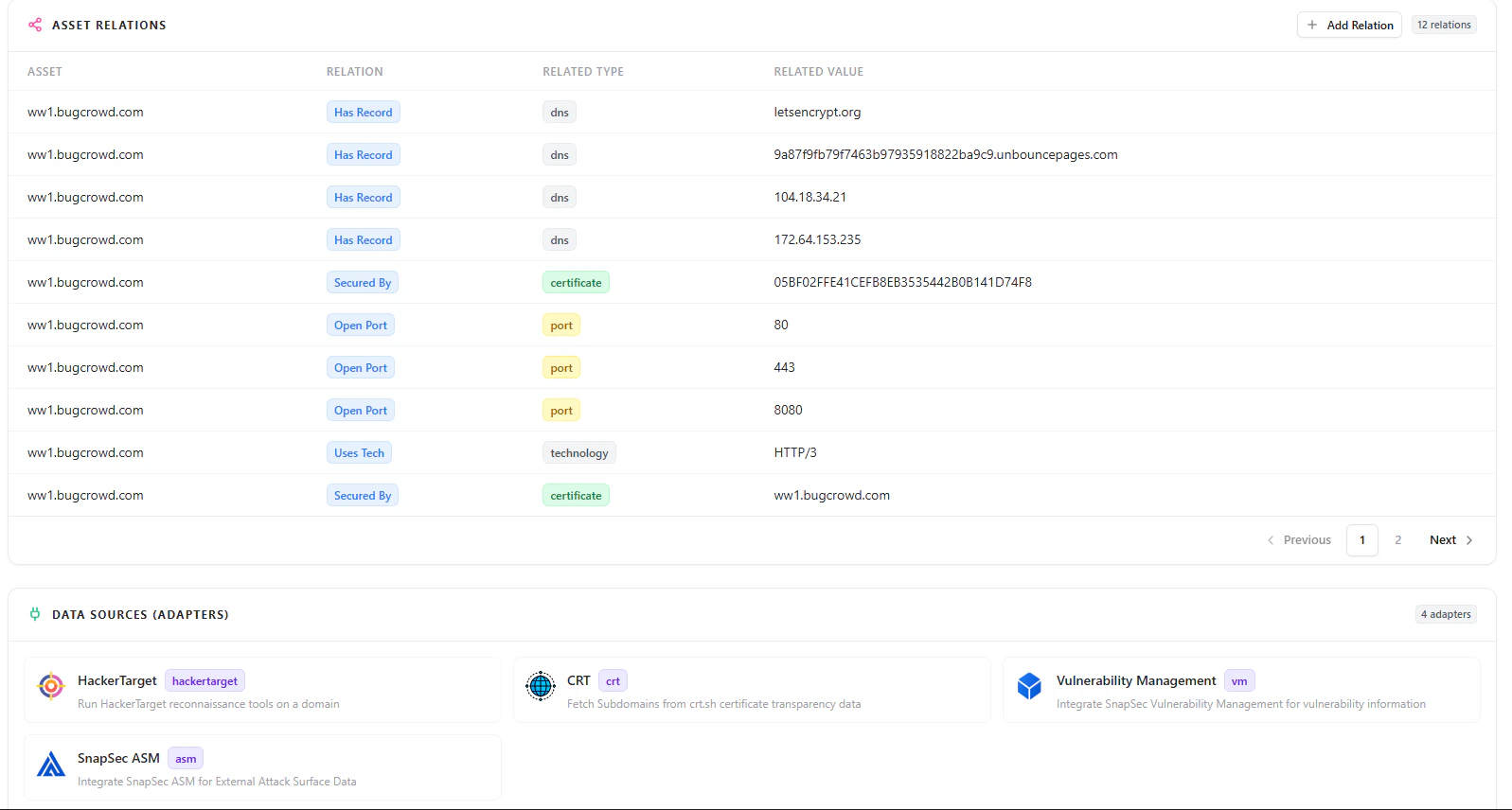
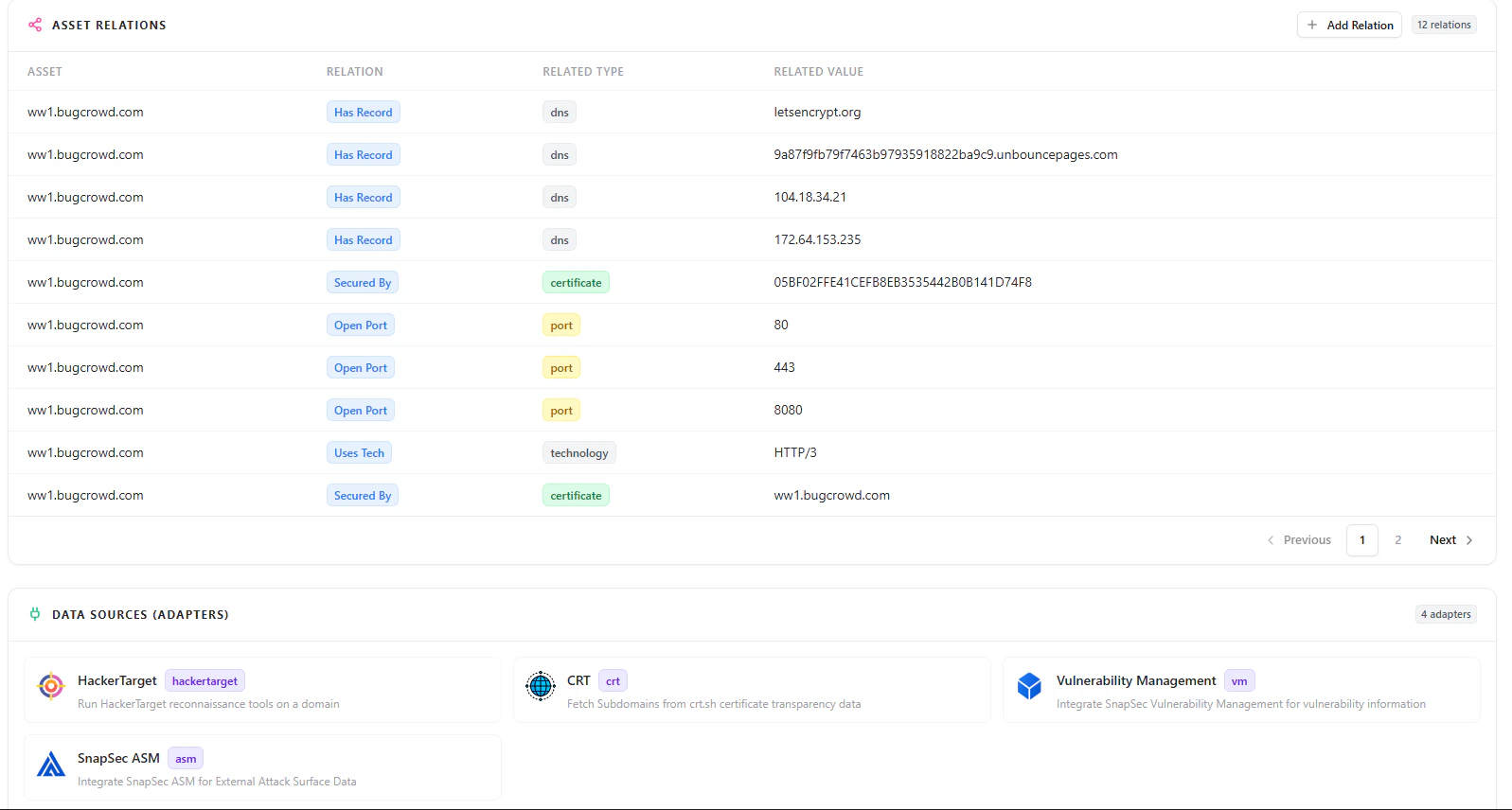
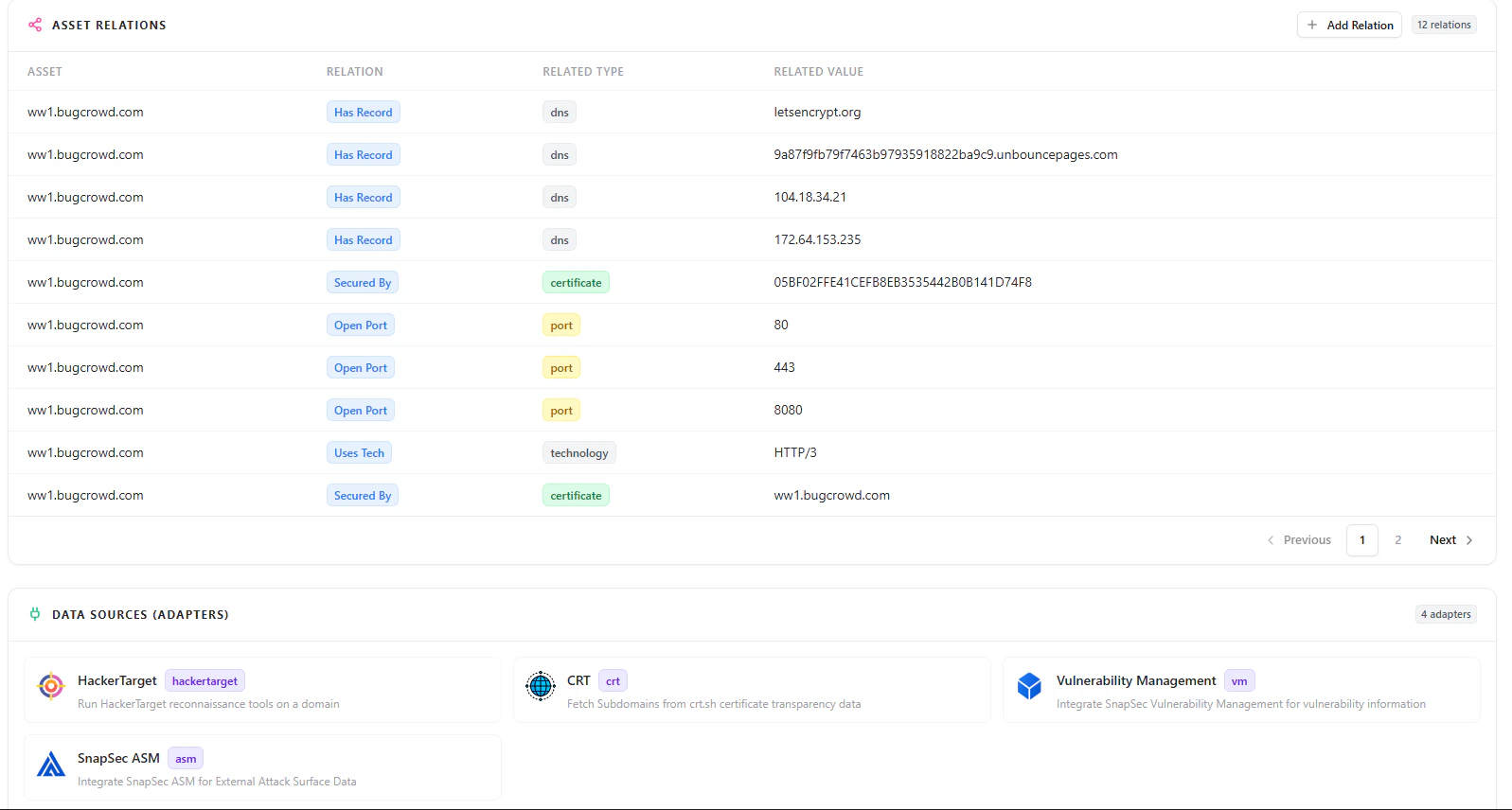
Asset Relationships
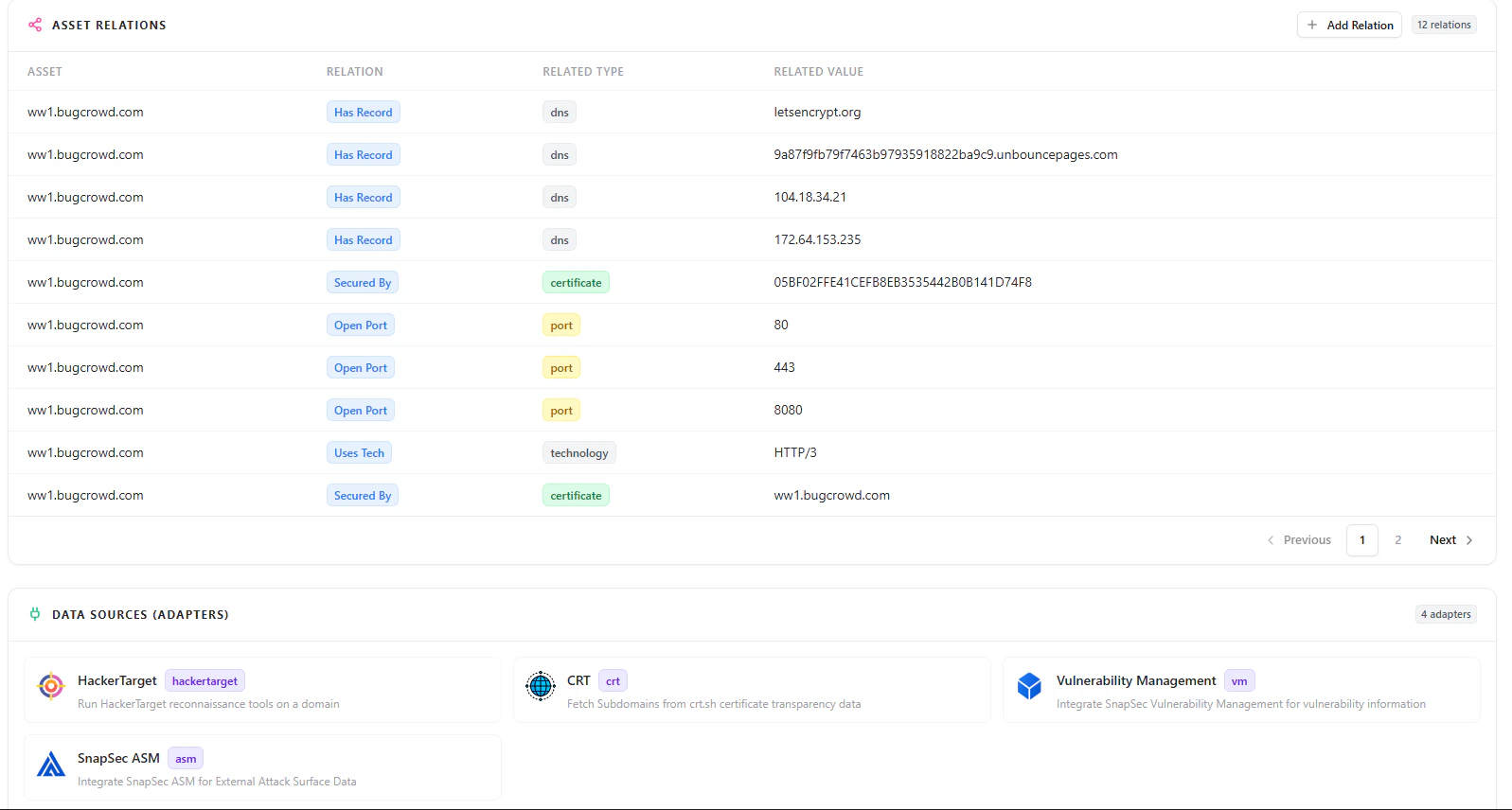
Data Sources
Why This Matters
- Prevents orphaned and unmanaged assets
- Enables safe decommissioning without losing context
- Allows quick restoration of critical assets
- Maintains full lifecycle visibility across infrastructure
- Preserves security, ownership, and operational history
Explore Live Demo
Explore AIM Live — No Signup Needed
Experience how Snapsec AIM helps you manage asset states, restore assets instantly, and maintain complete lifecycle visibility across your infrastructure.