Documentation Index
Fetch the complete documentation index at: https://docs.snapsec.co/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Detection Rules are the core of how vulnerabilities are identified. They simulate attacker behavior by modifying requests and analyzing responses to detect security flaws.Rule Categories
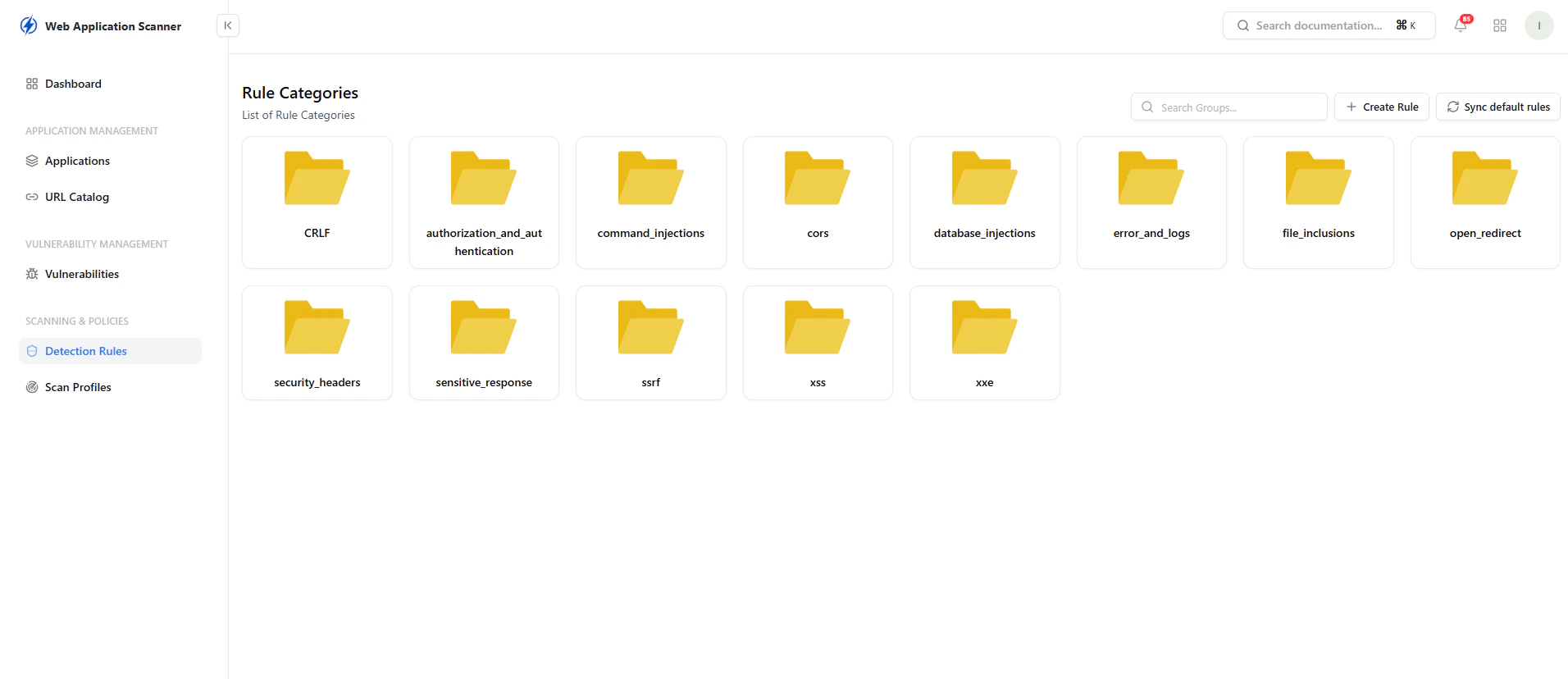
- CRLF
- Authentication & Authorization
- Command Injection
- CORS
- Database Injection
- Error Handling & Logs
- File Inclusion
- Open Redirect
- Security Headers
- Sensitive Data Exposure
- SSRF
- XSS
- XXE
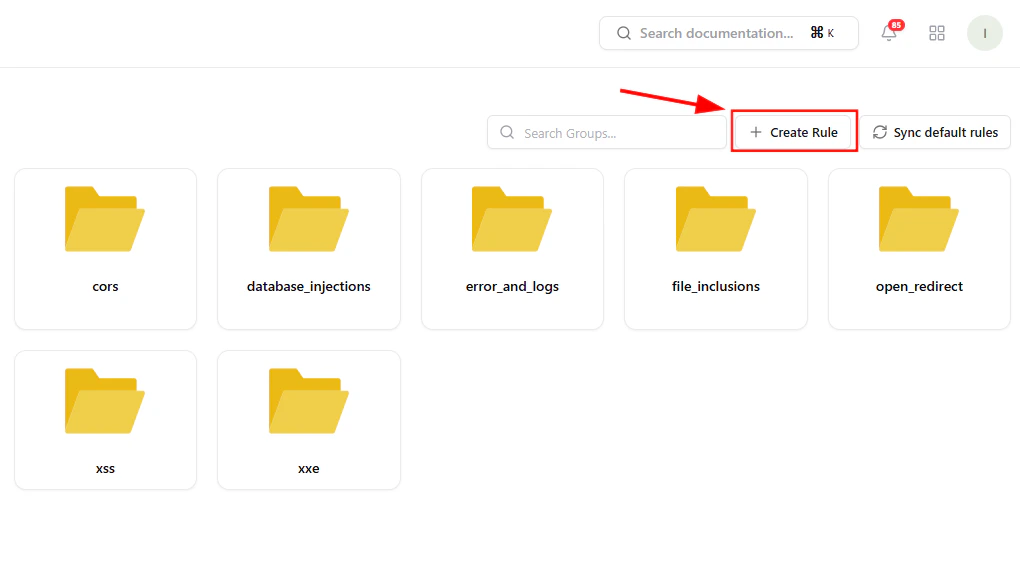
Creating a Rule
YAML-Based Rule Engine
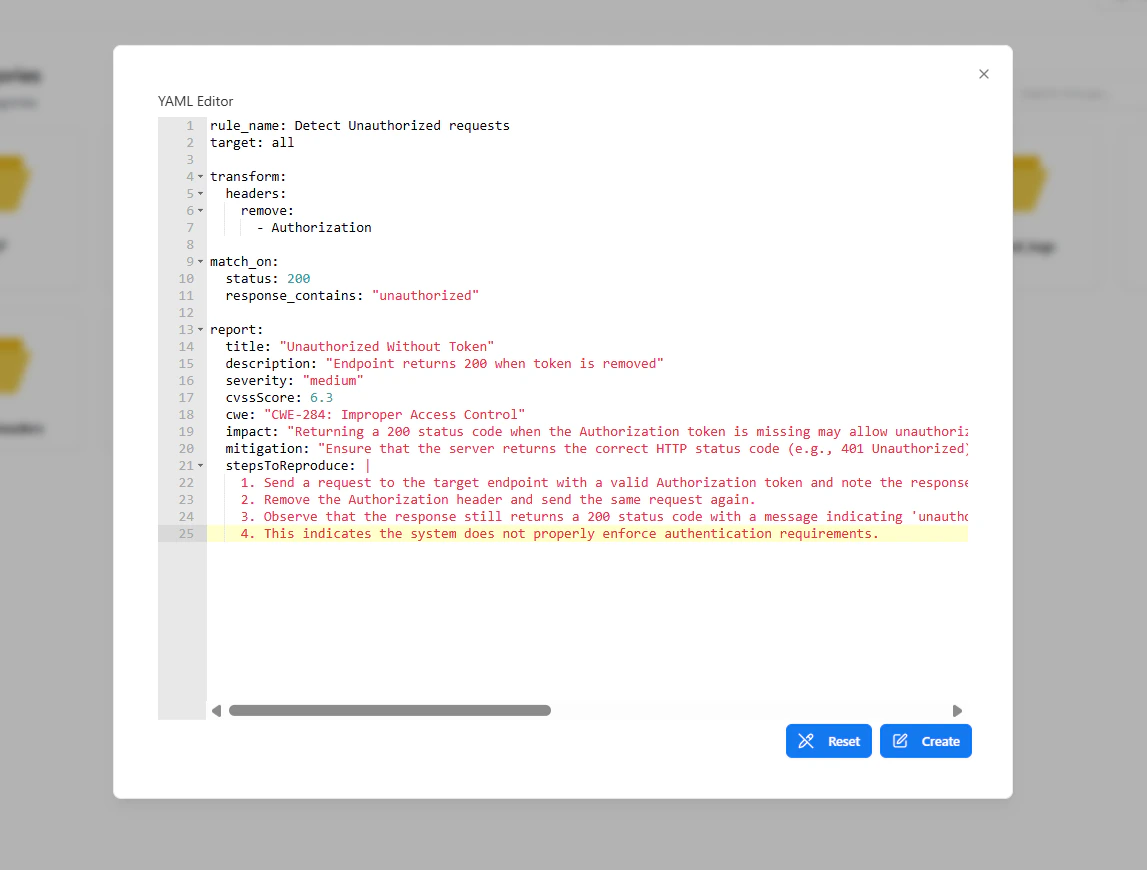
Core Sections
- Transform
- Modify headers, query params, or body
- Match Conditions
- Status codes
- Response content
- Report
- Title
- Description
- Severity
- CWE
- CVSS
- Impact
- Mitigation
- Reproduction Steps
Rule Execution Logic
Rules work by:- Modifying the original request
- Sending the transformed request
- Analyzing the response
- Flagging unexpected behavior as vulnerabilities
Rule Management
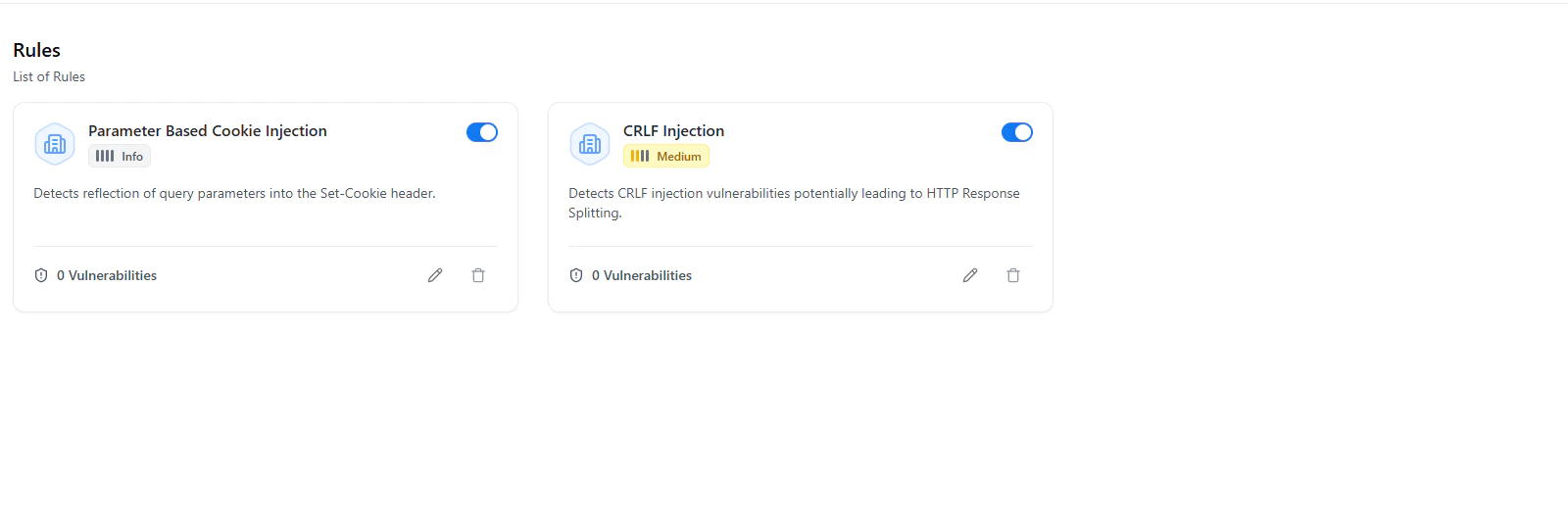
- Enable / Disable toggle
- Severity classification
- Detection description
- Number of findings
Editing Rules
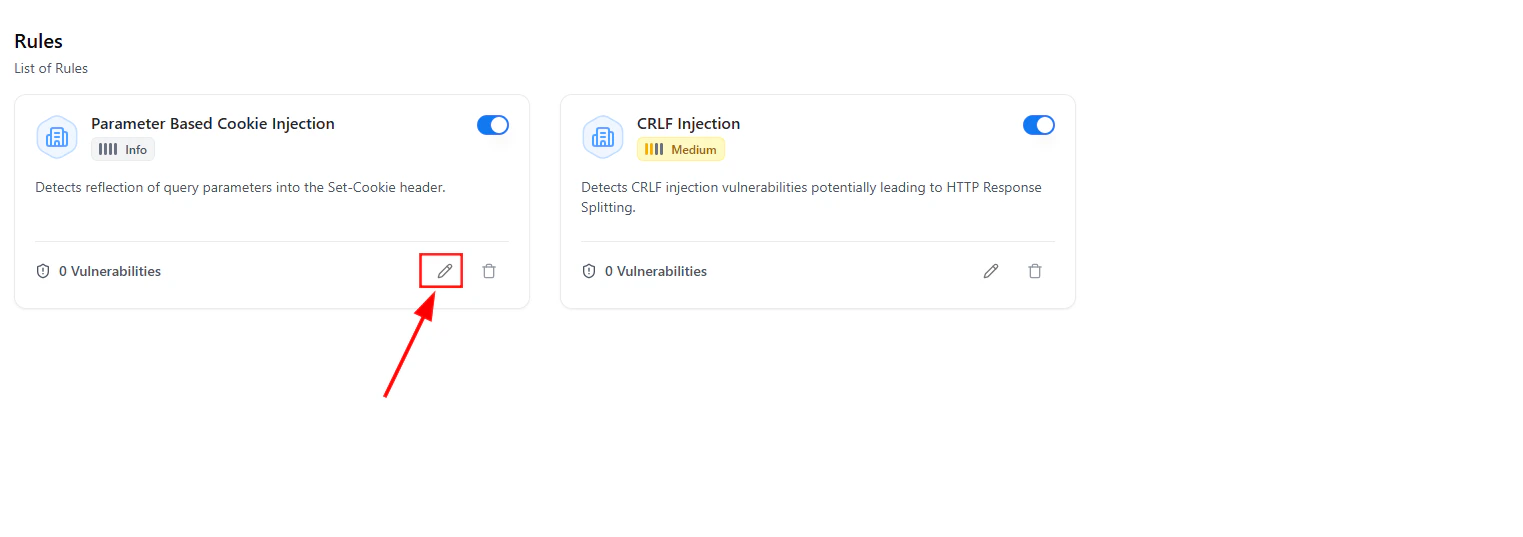
- Improve detection accuracy
- Reduce false positives
- Adjust logic for application-specific behavior
Deep Rule Customization
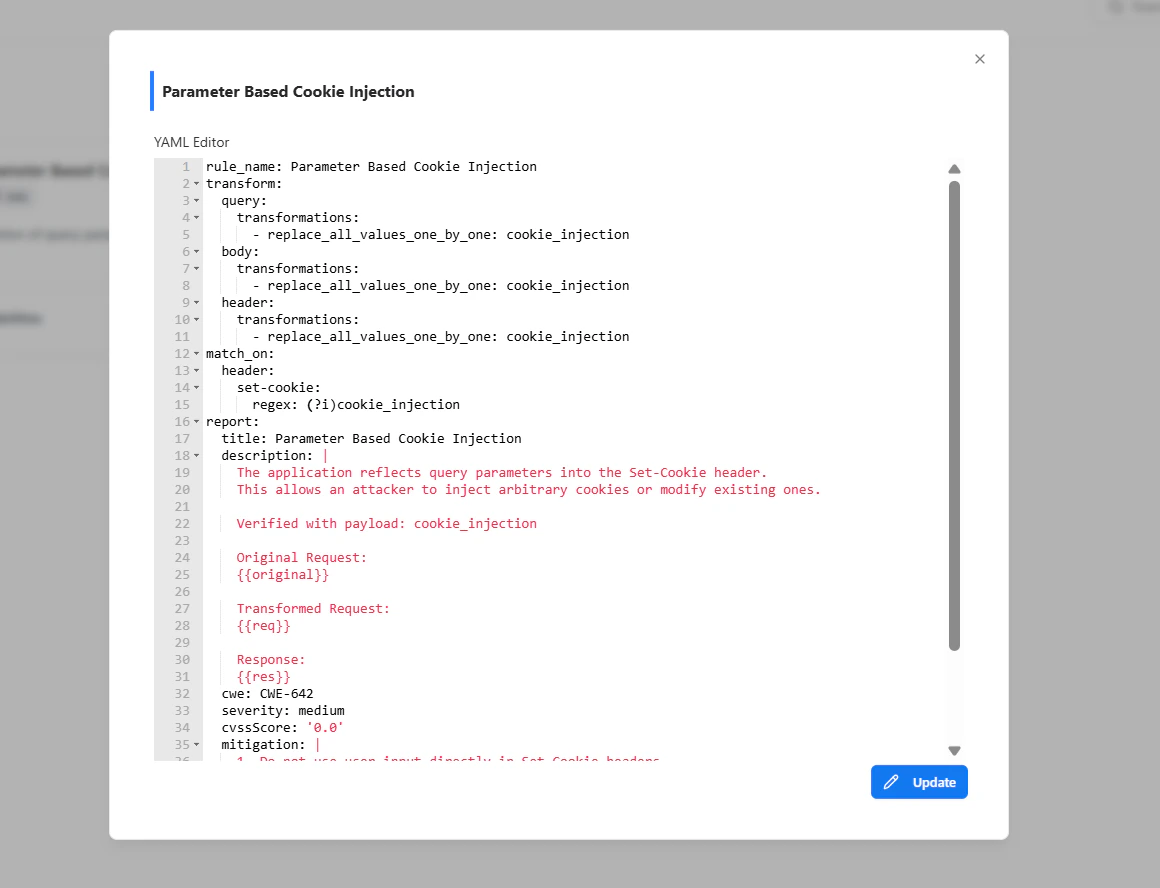
- Request transformations
- Matching conditions
- Reporting output
- Business logic flaws
- Authorization bypass
- Misconfigurations
- Edge-case vulnerabilities
Why It Matters
Detection Rules turn your scanner into a customizable security engine.Key Benefits
- Adapt scanning to your application logic
- Detect beyond standard vulnerability signatures
- Reduce noise with precise matching
- Align findings with real-world attack patterns
- Enable security teams to build reusable detection logic
Explore Live Demo
Build Your Own Detection Rules
Create, test, and deploy custom detection logic tailored to your applications.