Documentation Index
Fetch the complete documentation index at: https://docs.snapsec.co/llms.txt
Use this file to discover all available pages before exploring further.
Overview
The Reports section allows security teams to generate, manage, and export structured reports of their external attack surface. Reports consolidate data from scans, assets, and risk signals into executive-ready and audit-friendly documents, enabling better visibility, decision-making, and compliance tracking.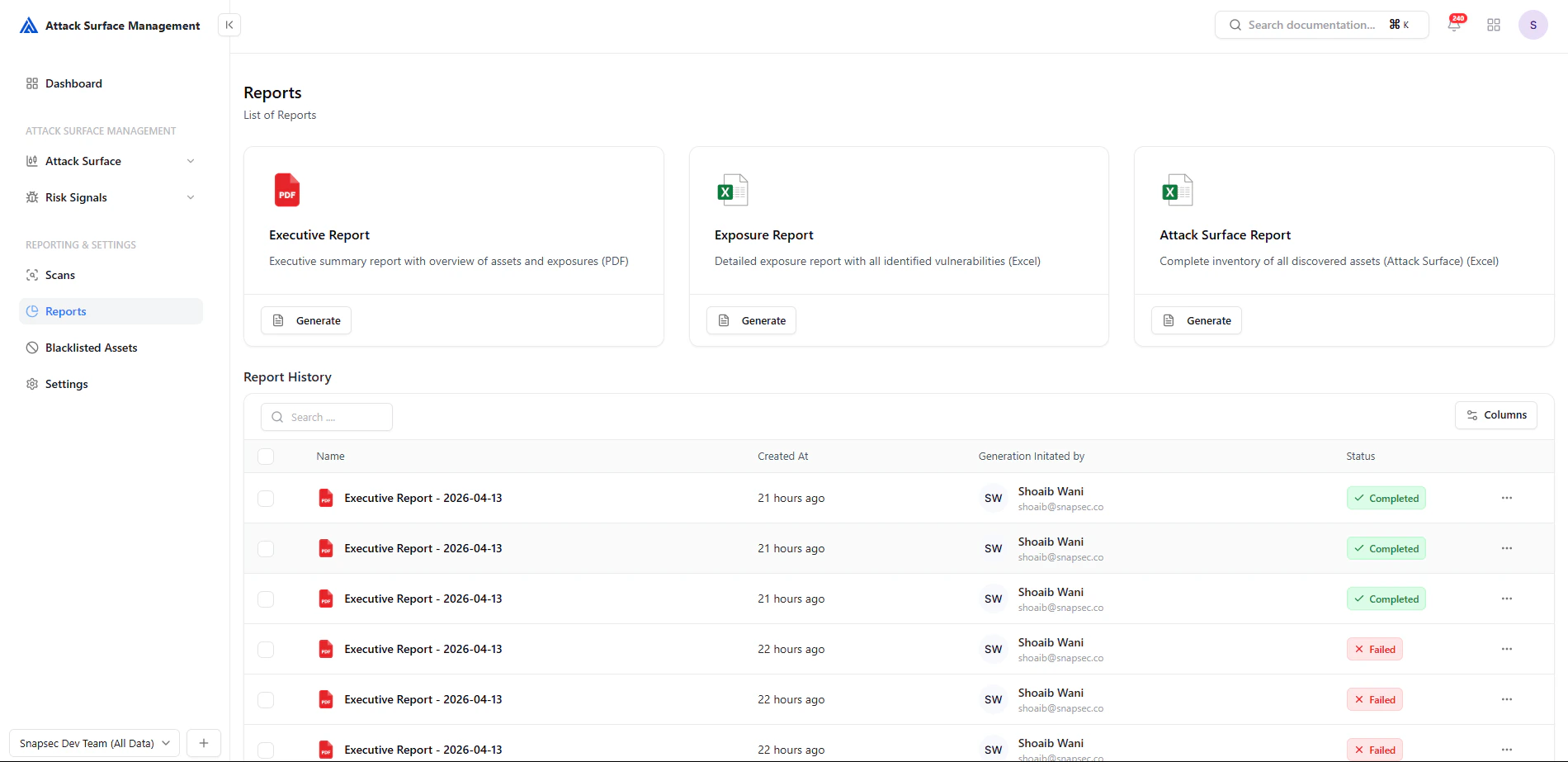
Report Types
The platform supports multiple report formats tailored for different use cases:Executive Report
High-level PDF report summarizing assets, exposures, and risk posture for leadership and stakeholders.
Exposure Report
Detailed breakdown of all detected exposures and vulnerabilities in structured format.
Attack Surface Report
Complete inventory of all discovered external assets across your organization.
Generating Reports
To generate a report:- Select the desired report type
- Click Generate
- The system compiles data from scans and exposures
- Report appears in Report History
Report History
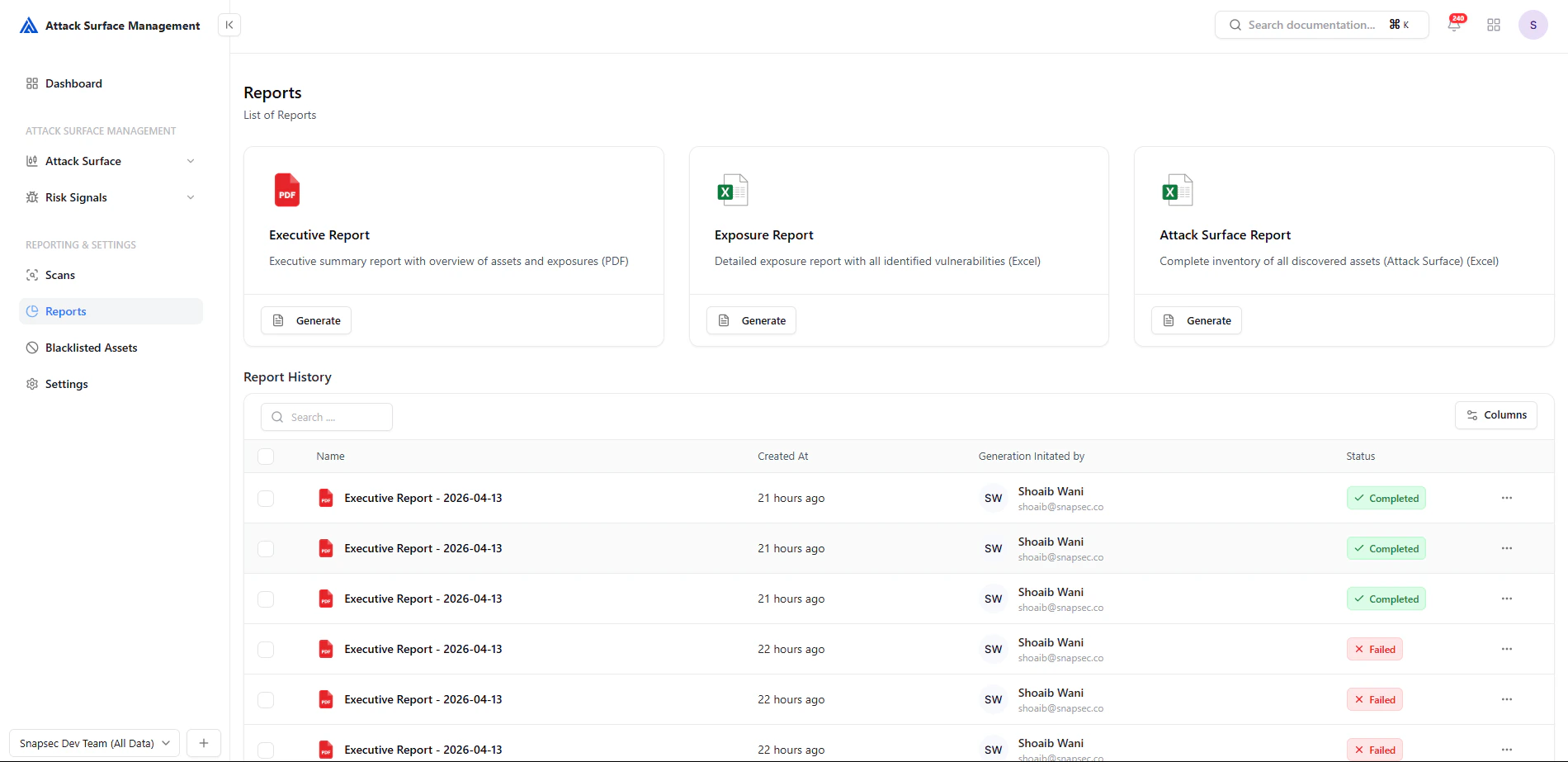
Fields Explained
| Field | Description |
|---|---|
| Name | Report title with timestamp |
| Created At | When the report was generated |
| Generation Initiated By | User who triggered the report |
| Status | Current state (Completed / Failed) |
Report Status
- 🟢 Completed — Report is ready for download
- 🔴 Failed — Report generation failed
- 🟡 (Processing) — Report is being generated (if applicable)
Report Actions
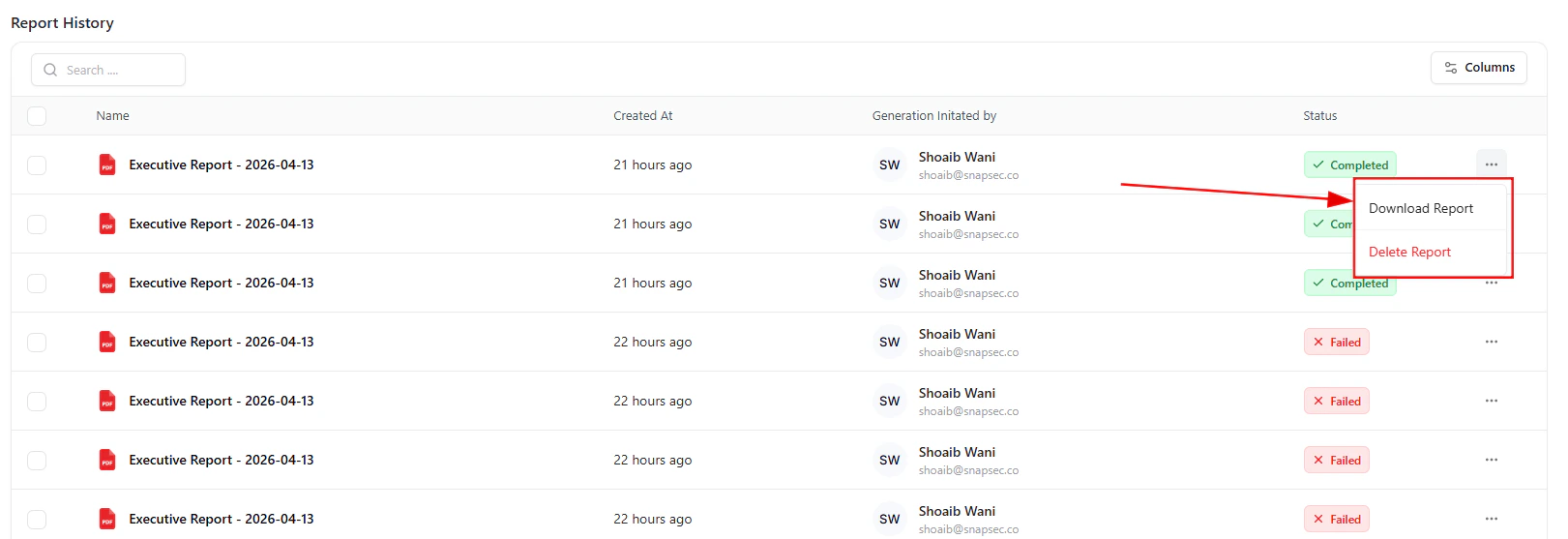
- ⬇️ Download Report — Export the report file
- 🗑️ Delete Report — Remove unnecessary reports
How Reports Are Built
Reports aggregate data from multiple ASM components:- Scans — Asset discovery results
- Assets — Subdomains, IPs, services
- Exposures — Detected risks and misconfigurations
- Risk Signals — Correlated findings and severity
Workflow Example
- Run or complete a scan
- Navigate to Reports
- Generate an Executive or Exposure report
- Wait for processing to complete
- Download and share with stakeholders
Benefits
- ✅ Centralized reporting for all ASM data
- ✅ Executive-ready summaries
- ✅ Easy export for compliance and audits
- ✅ Full audit trail of generated reports
- ✅ Quick access to historical reports
Best Practices
- 📅 Generate reports after each major scan
- 📊 Use Executive Reports for leadership
- 🔍 Use Exposure Reports for technical teams
- 🧹 Clean up failed or duplicate reports regularly
From Data to Decisions
Scan → Detect → Analyze → Report → Act Reports transform raw attack surface data into actionable insights for both technical and non-technical stakeholders.Explore Live Demo
Explore ASM Live — No Signup Needed
Instantly explore how Snapsec Attack Surface Management (ASM) detects exposures, correlates signals, and enables real-time security decisions — all in one unified platform.